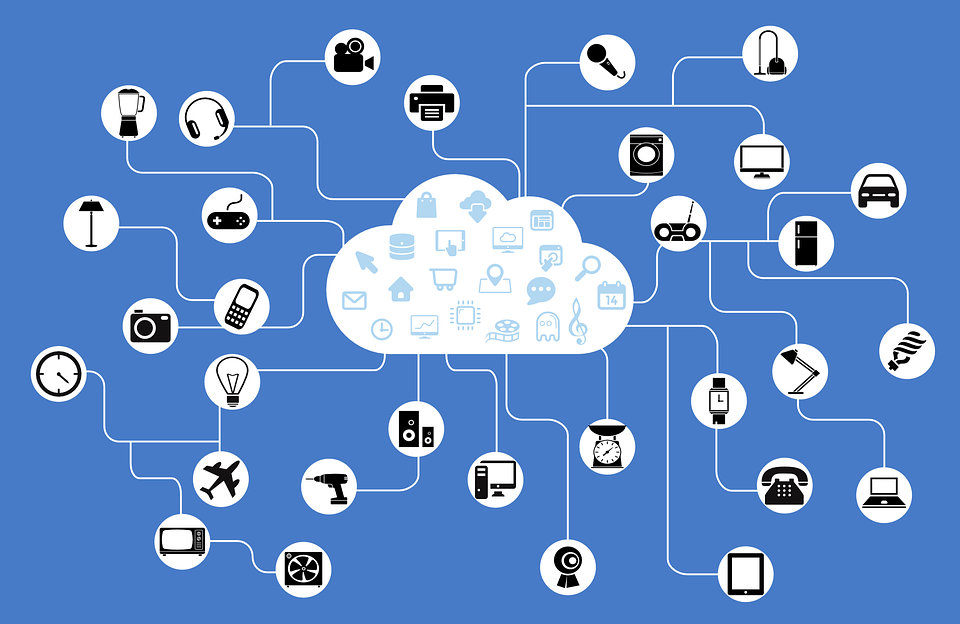
 When establishing defensive measures to secure their enterprise, many organizations often overlook a key element – those outside of their network, but who are still connected to their digital ecosystem. In other words, any vendor, supplier, partner, or third party who is relied on as part of an organization’s functionality, and who has access to one or more of a company’s information systems or facilities, stores confidential entity information on their systems, or otherwise provides services to, or on behalf of the entity.
When establishing defensive measures to secure their enterprise, many organizations often overlook a key element – those outside of their network, but who are still connected to their digital ecosystem. In other words, any vendor, supplier, partner, or third party who is relied on as part of an organization’s functionality, and who has access to one or more of a company’s information systems or facilities, stores confidential entity information on their systems, or otherwise provides services to, or on behalf of the entity.
If a connected third party has poor security, your own threat mitigation tactics are largely irrelevant. Their vulnerabilities are your vulnerabilities, meaning you’re not only responsible for your own security program, but anyone else’s who is connected as well.
Malicious actors are well aware of these potential weak links and are increasingly using them as points of entry, as 56% of organizations are breached because of a vendor, according to a recent Ponemon/Opus survey of more than 15,000 people. The same survey also revealed that almost 60% of organizations are unable to determine if their vendor security is sufficient. This is a dangerous combination, so we’ve put together a quick list of what you can do today to begin shoring up gaps created by third parties.
- Dependencies and Diligence
Start with assessing the criticality of dependencies on services and products and then assess the security and risks around those dependencies. Which third parties are essential to your business continuity and what potential threats do they carry?
- Aggregate and Communicate
Once the dependencies on your third parties is assessed, you then need to compare their risk profiles and prioritize their overall impact on your enterprise. For example, an organization who sells a product online and uses a vendor to provide internet service should prioritize this relationship over a company they use to shred their old documents.
- Go Through the Risk Management Process
It’s not always going to be possible to mitigate, transfer, or avoid risk entirely, and sometimes it’s okay to accept certain risks. As long as you are aware of what you are accepting and the corresponding consequences, it’s not always necessary (or possible) to transfer the risk. However, be sure to translate any of these risk management decisions into contractual agreements so that both parties involved are aware of the arrangement.
- Periodically and Independently Assess Vendors
You need to ensure that your third parties are actually practicing what they preach. By entering into a service agreement with them, you are accepting whatever risk they carry, whether you are aware of it or not.
Once these steps have been taken and you have a better grasp of your third-party cyber risk, don’t stop there. This management is an ongoing process that should include the following:
- Conduct regular site visits to observe controls
- Inspect results of internal audits
- Require policy/procedure documentation and proof of security testing
- Administer discussions with third parties and their employees
- Assess whether contractual agreements match the entity’s policies
Managing third-party cyber risk isn’t easy, but the process is also not too complex. A dedicated, team-effort of understanding and prioritizing potential threats from your connected vendors will go a long way towards shoring up your enterprise.